-
Website chỉ bán hàng online từ tháng 8/2024 - Giao hàng toàn quốc
- sachonthidh@gmail.com
A Guide to Kernel Exploitation: Attacking the Core 1st Edition
Mã sản phẩm: aGtKE1stGiao hàng và Khuyến mãi
Hỗ trợ tư vấn sách, tìm sách, xem chi tiết đơn hàng, thay đổi thông tin, thanh toán online QR code qua kênh facebook ICTBook Nhà Sách Lập Trình Chat với CSKH ấn vào đây
Được kiểm tra hàng khi giao hàng. Thời gian vận chuyển miền Bắc 2-3 ngày, miền Nam 3-5 ngày. Chuẩn bị hàng trung bình 1 ngày.
Chú ý: Đơn hàng được giao bởi hãng vận chuyển Shopee Express, bưu tá giao hàng chung với các đơn trên sàn shopee. Khi nhận hàng quý khách kiểm tra trên nhãn vận đơn shop đã ghi chi tiết sản phẩm
- Nếu khách đăng nhập tài khoản trên website này thì có thể tự quản lý các đơn đã mua, xem chi tiết đơn. Nếu khách vãng lai không đăng nhập thì sau khi đặt hàng chỉ tra cứu được mã hóa đơn và tổng tiền, khách vãng lai cần xem chi tiết đơn thì nhắn tin qua Facebook.
- Sản phẩm là CÒN HÀNG nếu có hiển thị 2 nút "MUA NGAY" và "THÊM VÀO GIỎ HÀNG" tại trang này. Sản phẩm hết hàng, không hiển thị nút đặt hàng =>Nếu còn hàng vui lòng không hỏi lại nhân viên, nếu hết hàng hãy liên hệ Chat với shop.
- Cách đặt hàng: nhấn THÊM VÀO GIỎ HÀNG rồi tiếp tục lựa chọn các sách khác, chọn sách xong vào Giỏ hàng và điền thông tin Đặt hàng. Điền đủ các thông tin người nhận, chọn phương thức thanh toán và kiểm tra kĩ tổng số lượng, phí ship.
- Tra cứu tại mục Tra cứu đơn hàng. Khi cần hỗ trợ gấp gọi ĐT hoặc nhắn tin facebook phía cuối trang web
Mô tả sản phẩm
Publisher : Syngress; 1st edition (September 29, 2010)
Language : English
Paperback : 464 pages
ISBN-10 : 1597494860
ISBN-13 : 978-1597494861
Chi tiết sản phẩm
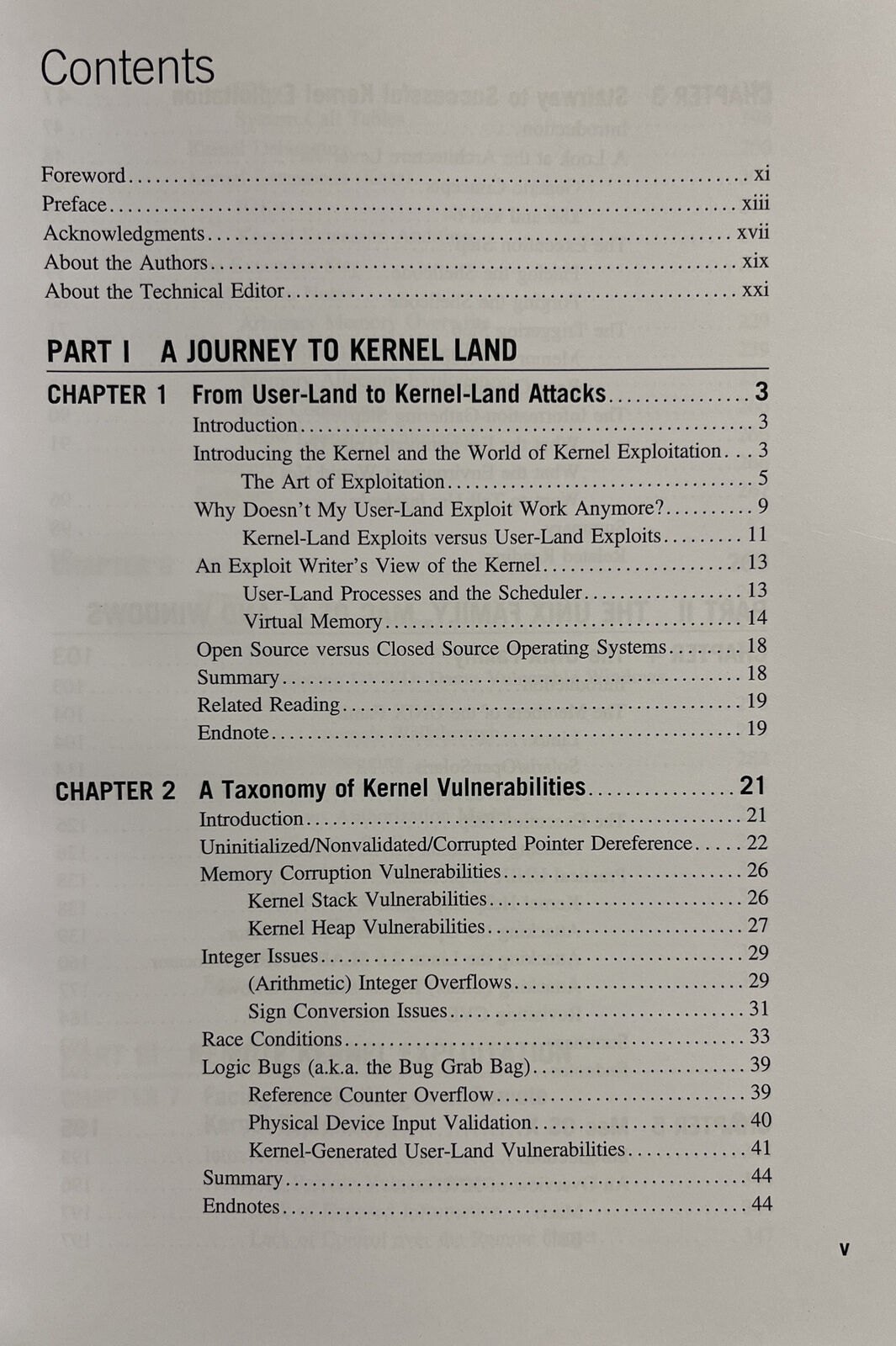
A Guide to Kernel Exploitation: Attacking the Core discusses the theoretical techniques and approaches needed to develop reliable and effective kernel-level exploits, and applies them to different operating systems, namely, UNIX derivatives, Mac OS X, and Windows. Concepts and tactics are presented categorically so that even when a specifically detailed vulnerability has been patched, the foundational information provided will help hackers in writing a newer, better attack; or help pen testers, auditors, and the like develop a more concrete design and defensive structure.
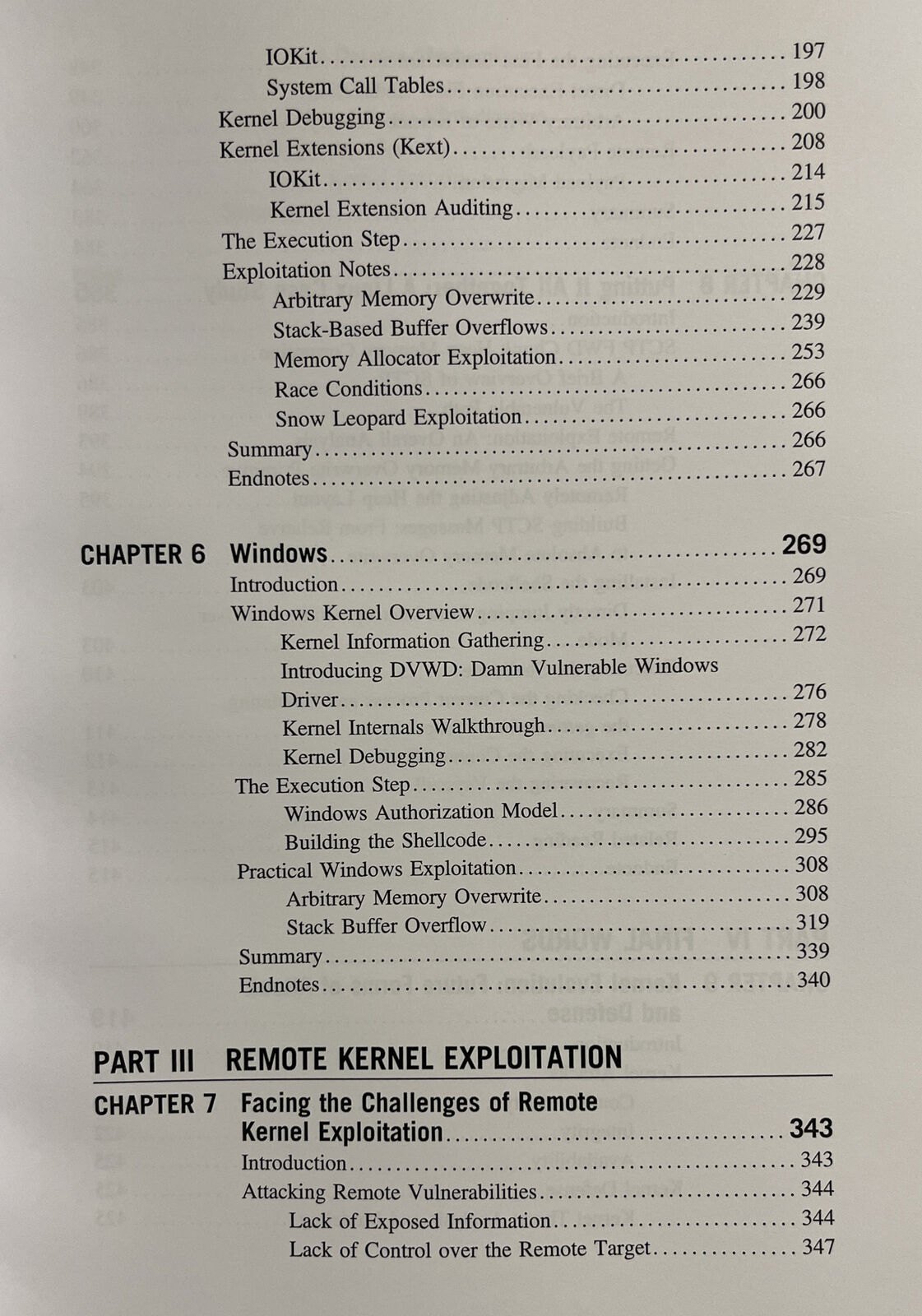
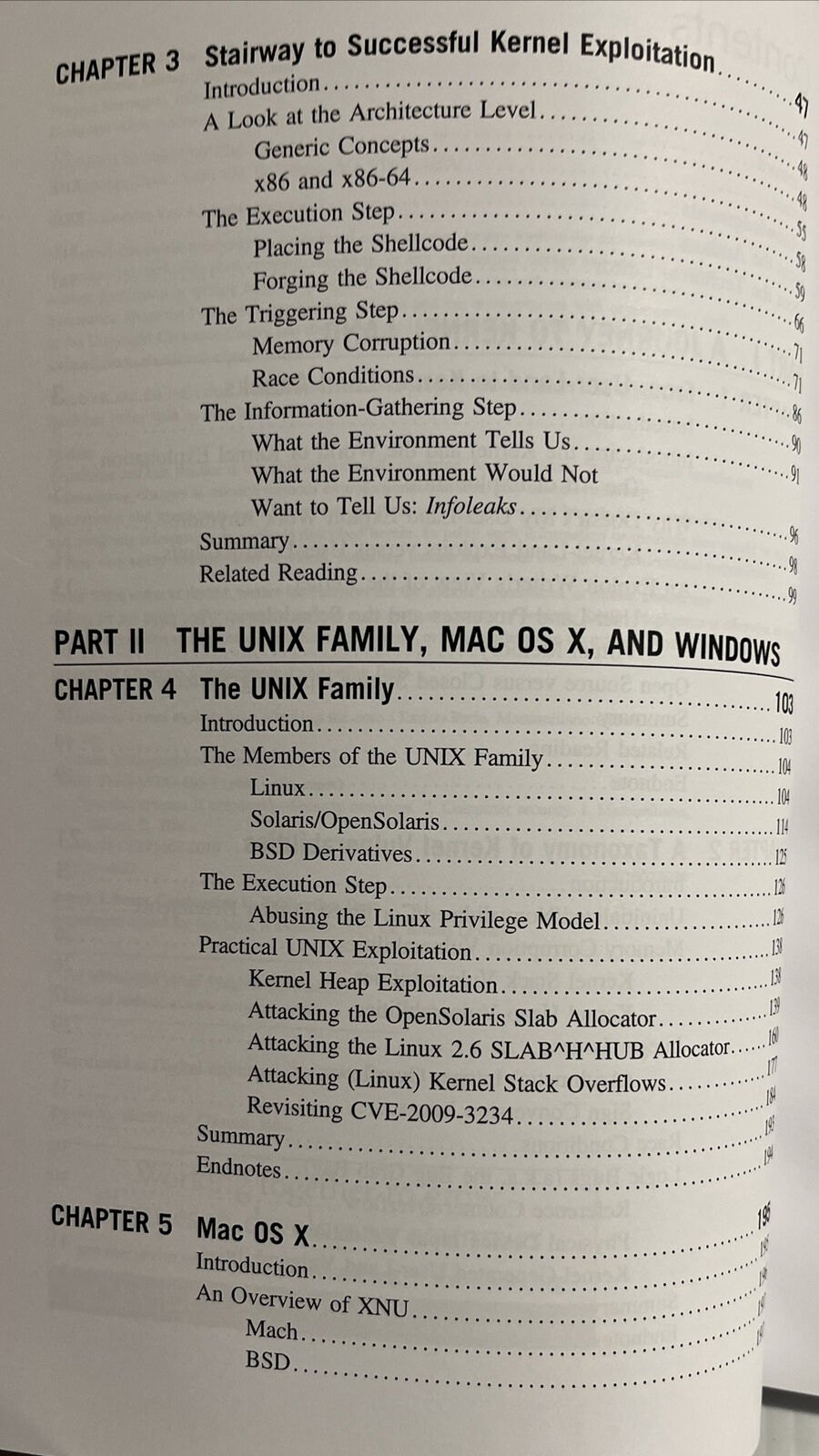
The book is organized into four parts. Part I introduces the kernel and sets out the theoretical basis on which to build the rest of the book. Part II focuses on different operating systems and describes exploits for them that target various bug classes. Part III on remote kernel exploitation analyzes the effects of the remote scenario and presents new techniques to target remote issues. It includes a step-by-step analysis of the development of a reliable, one-shot, remote exploit for a real vulnerabilitya bug affecting the SCTP subsystem found in the Linux kernel. Finally, Part IV wraps up the analysis on kernel exploitation and looks at what the future may hold.
- Covers a range of operating system families ― UNIX derivatives, Mac OS X, Windows
- Details common scenarios such as generic memory corruption (stack overflow, heap overflow, etc.) issues, logical bugs and race conditions
- Delivers the reader from user-land exploitation to the world of kernel-land (OS) exploits/attacks, with a particular focus on the steps that lead to the creation of successful techniques, in order to give to the reader something more than just a set of tricks
Review
"A very interesting book that not only exposes readers to kernel exploitation techniques, but also deeply motivates the study of operating systems internals, moving such study far beyond simple curiosity."--Golden G. Richard III, Ph.D., Professor of Computer Science, University of New Orleans and CTO, Digital Forensics Solutions, LLC
Review
From the Back Cover
About the Author
Massimiliano Oldani currently works as a Security Consultant at Emaze Networks. His main research topics include operating system security and kernel vulnerabilities.





Nhận xét đánh giá